System Calls in Linux
 Linux System Calls and their Numbers
Linux System Calls and their Numbers
System Calls
System calls are a special set of procedures that regular programs (user space processes) can submit to the Linux kernel for working with files, interacting with hardware, accessing internal OS functionality, implement all sorts of communication and process management and basically do anything else that’s sensitive or performance critical enough that OS kernel must enforce strict controls around it.
Regular processes interface with the OS kernel by supplying a system call name and parameters, the kernel then verifies validity of a system call and executes it within kernel space, returning data and execution status back.
Each system call has a unique number and name for identification. There are separate syscall numbers for 32bit and 64bit architectures.
System Calls in Linux
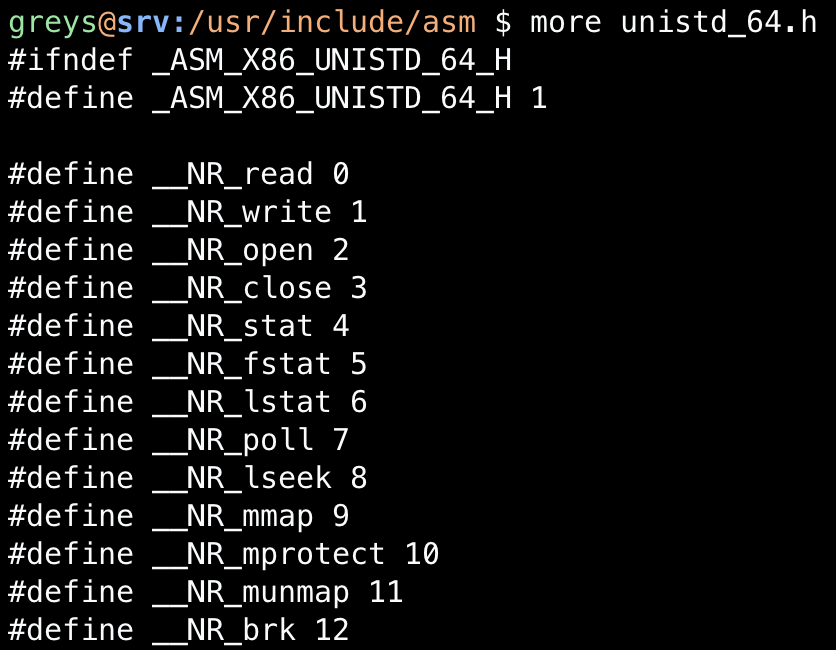
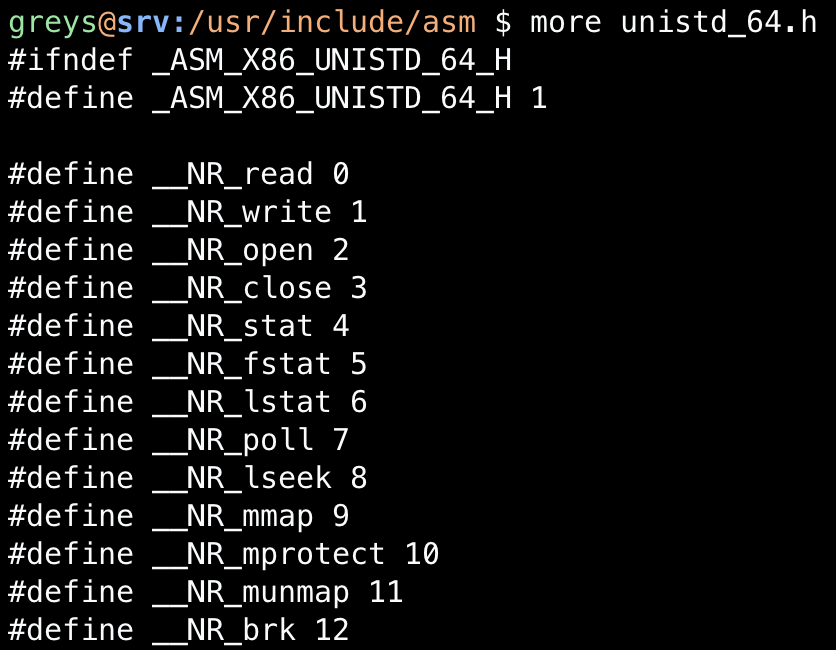
To review the full list of system calls in your Linux distribution, you’ll need to inspect the unistd-32.h or unistd-64.h file.
In CentOS and RedHat, this file is installed by the kernel-headers package.
When browsing the file, you’ll see a list like this:
greys@srv:~ $ less /usr/include/asm/unistd_32.h
#ifndef \_ASM_X86_UNISTD_32_H
#define \_ASM_X86_UNISTD_32_H 1
#define **NR_restart_syscall 0
#define **NR_exit 1
#define **NR_fork 2
#define **NR_read 3
#define **NR_write 4
#define **NR_open 5
#define **NR_close 6
#define **NR_waitpid 7
#define **NR_creat 8
#define **NR_link 9
#define **NR_unlink 10
#define **NR_execve 11
#define **NR_chdir 12
#define **NR_time 13
#define **NR_mknod 14
#define **NR_chmod 15
#define **NR_lchown 16
#define **NR_break 17
#define **NR_oldstat 18
#define **NR_lseek 19
#define **NR_getpid 20
#define **NR_mount 21
#define **NR_umount 22
#define **NR_setuid 23
#define **NR_getuid 24
#define **NR_stime 25
#define **NR_ptrace 26
#define **NR_alarm 27
#define **NR_oldfstat 28
#define **NR_pause 29
#define **NR_utime 30
#define **NR_stty 31
#define **NR_gtty 32
#define **NR_access 33
#define **NR_nice 34
#define **NR_ftime 35
#define **NR_sync 36
#define **NR_kill 37
...
For instance, __NR_mount indicates the syscall name - the actual name is the word without __NR_ bit, so in this case it’s mount. 21 is the syscall number in your Linux.
Syscall Man Pages
To get more information about using a system call, just use man command. Because syscalls are a pretty core part of man pages, they have their own section - it’s section number 2. So add .2 to the name of a syscall when looking for it:
greys@srv:~ $ man mount.2
MOUNT(2) Linux Programmer's Manual MOUNT(2)
NAME
mount - mount filesystem
SYNOPSIS
#include <sys/mount.h>
int mount(const char *source, const char *target,
const char *filesystemtype, unsigned long mountflags,
const void *data);
DESCRIPTION
mount() attaches the filesystem specified by source (which is often a pathname referring to a device, but can also be the pathname of a directory or file, or a dummy string)
to the location (a directory or file) specified by the pathname in target.
Appropriate privilege (Linux: the CAP_SYS_ADMIN capability) is required to mount filesystems.
Values for the filesystemtype argument supported by the kernel are listed in /proc/filesystems (e.g., "btrfs", "ext4", "jfs", "xfs", "vfat", "fuse", "tmpfs", "cgroup",
"proc", "mqueue", "nfs", "cifs", "iso9660"). Further types may become available when the appropriate modules are loaded.
The data argument is interpreted by the different filesystems. Typically it is a string of comma-separated options understood by this filesystem. See mount(8) for details
of the options available for each filesystem type.
SysCall Numbers
Don’t forget: although oldest syscalls match across multiple distributions, there’s always a chance that a particular syscall will have a different number in your OS.
This is only relevant if you’re trying to use syscalls directly - which you probably shouldn’t. Use glibc instead - I’ll be sure to write a small article on it sometime in the future.
See Also
- Linux Kernel
- Unix Tutorial Digests
- Linux Kernel 5.8
- Confirm current Kernel boot command
- Linux Commands
- Unix Commands
- Where to Find Syscall Numbers






